Key Moments
The Internet Was Weeks Away From Disaster and No One Knew
Key Moments
Backdoor in XZ compromised OpenSSH; Linux at risk for years.
Key Insights
The XZ backdoor shows how a single maintenance bottleneck in open-source tooling can threaten vast parts of the internet via shared libraries and dependencies.
Open-source ecosystems rely on many small, volunteer-maintained components; if one link wobbles, millions of systems can be affected.
Attackers exploited the loader and dynamic linking process (global offset table, audit hooks) to hijack RSA decryption without immediately breaking existing code paths.
A three-step intrusion (Trojan in XZ, Goldilocks window in the linker, Cat Burglar backdoor) demonstrates how stealth can be achieved inside legitimate software chains.
Security by abstraction (open review) is powerful, but also requires vigilant, diverse scrutiny; discovery often comes from unusual performance or behavior signals rather than obvious code flaws.
attribution remains uncertain, but analysts lean toward state-backed or highly resourced actors; regardless, the incident underscores the need for stronger supply-chain defenses.
OPEN SOURCE, FREEDOM, AND THE HARD REALITIES
Open source emerged from a culture of sharing and collaboration, letting communities build software from freely inspectable code. This led to astonishing scale: Linux runs most servers, Android, nuclear submarines, and many critical systems rely on open components. Yet the same openness creates fragile dependence on a mosaic of volunteer-maintained tools. The Xerox printer anecdote and Stallman’s move to promote four freedoms show a tension: freedom enables rapid progress, but a system can hinge on a single maintainer whose burnout or withdrawal risks cascading failures across the internet.
SSH, OPENSSH, AND THE MASTER KEY
Secure remote login became essential as machines proliferated far beyond human-facing consoles. SSH, and particularly the OpenSSH implementation, became the backbone for remote administration; its security is under constant scrutiny because a flaw here can grant universal access. The open-source model concentrates many eyes on core code, but the vulnerability surface extends through dependencies and shared libraries. The goal of SSH is trust: a robust handshake plus authenticated keys, yet the entire trust chain can be undermined if a dependent component is compromised.
THE XZ BACKDOOR: FROM COMPRESSOR TO COMPROMISE
XZ is a lossless compression library with deep Linux integration; it gained prominence because efficient updates mean smaller transfers across millions of machines. The backdoor story centers on a long game: a stealthy attacker weathers years of testing, social engineering, and dependency chaining to inject a dangerous payload into XZ. The plan relied on the fact that XZ sits in the dependency chain of OpenSSH; by compromising XZ, the attacker could plant a foothold across many Linux deployments without overtly altering core SSH code.
THE GOLDILOCKS ZONE: MEMORY MANAGEMENT AND AUDIT HOOKS
The attack hinges on a precise moment in memory and linker behavior. Shared libraries rely on the global offset table; attackers can use dynamic audit hooks to intercept and modify symbol resolution as the loader writes real addresses. By coordinating a payload insertion within a narrow window—before the table becomes read-only—the attacker can substitute RSA decrypt with their own routine. This Goldilocks zone is incredibly narrow, making timing and access control essential for success and difficult to defend against without deep monitoring.
THREE-STEP INFILTRATION: TROJAN HORSE, GOLDILOCKS, CAT BURGLAR
The intrusion unfolds in three acts. First, Trojan Horse: the attacker hides a payload inside benign test data within XZ’s build artifacts. Second, Goldilocks: via a carefully timed dynamic linking and audit-hook exploit, the attacker swaps in a malicious RSA decrypt path. Third, Cat Burglar: with the backdoor operational, the attacker uses a cryptographic exchange to authenticate and maintain stealth, wiping traces and ensuring persistence while the system continues to function for legitimate users. This orchestrated sequence demonstrates how open-source chains can be exploited from inside.
DISCOVERY, RESPONSE, AND AFTERMATH: A COMMUNITY RISES TO THE CHALLENGE
The discovery came from an observant security researcher who noticed anomalous slowdowns and suspicious changes in a test artifact, followed by public security disclosures. Red Hat, Debian, and other distributors quickly rolled back affected releases, while researchers traced the exploit to XZ’s integration with OpenSSH. The response highlighted the strength and fragility of open-source ecosystems: when defenders act rapidly, the broader ecosystem can recover, but the episode also exposed gaps in supply-chain oversight and the need for stronger attribution and defensive tooling.
ATTRIBUTION, GEOPOLITICS, AND THE FUTURE OF INTERNET SECURITY
Speculation about the attacker points to nation-state actors or well-resourced groups; however, the exact identity remains uncertain. The broader takeaway is not about pinning blame but about acknowledging that backdoors in open-source tooling can enable near-unseen control of critical infrastructure. The incident reinforces the case for more robust supply-chain security, transparent incident reporting, and better tooling to detect unusual linker and memory behaviors. It also challenges the open-source ethos to balance openness with stronger, auditable defense mechanisms against future, more sophisticated intrusions.
Mentioned in This Episode
●Products
●Software & Apps
●Tools
●Organizations
●Concepts
●People Referenced
Open-source backdoor defense cheat sheet
Practical takeaways from this episode
Do This
Avoid This
Lossless data compression: key figures mentioned
Data extracted from this episode
| Technique | Description | Reported size result |
|---|---|---|
| Deflate (Huffman + LZ77) | Common web/file compression pipeline | 85% smaller than original (demo) |
| LZMA | Advanced dictionary-based scheme (Loosely tied to 70% ZIP size) | Can shrink files to about 70% of ZIP size |
| XZ | Lossless compression tool used across Linux | Widely adopted; forms dependency for OpenSSH |
Common Questions
A backdoor was embedded in the XZ compression tool and woven into OpenSSH dependencies, allowing attackers to tamper with RSA authentication. The exploit used a precise memory-path manipulation and an audit hook to slip code into the authentication flow before detection.
Topics
Mentioned in this video
Microsoft employee who notices the backdoor in Debian/open-source ecosystem and investigates.
Security researcher who uncovers the back door and publicizes it; credited for saving the ecosystem.
Character representing the attacker orchestrating the XZ backdoor injection.
Alias used by the attacker illustrating a long-running social-engineering and backdoor campaign.
Finnish maintainer of the XZ compression tool; central figure whose burnout creates a single-point risk.
Student who adopted GPL and created the Linux kernel, catalyzing the combined GNU/Linux ecosystem.
Fictionalized alias in the narrative for Linus Torvalds’ role in Linux history.
Founder of the Free Software Foundation; promoted four freedoms and licensing that underpin GNU and open source.
Artist referenced via the Never Gonna Give You Up lyric example used in the compression demonstration.
Helsinki researcher who introduced secure password practices and helped secure remote login.
Debian testing channel used to stage the updated XZ backdoor for broader testing.
Red Hat distribution used in testing and pre-release deployment scenarios for XZ updates.
Free software project started to promote four freedoms; key step toward copyleft licensing.
Open-source SSH implementation; backbone for remote machine access and a primary target via dependency exploitation.
Open-source database project referenced in the narrative; part of the broader ecosystem.
Ubuntu pre-release channel mentioned as a target for deploying the backdoor.
Lossless compression tool used widely in Linux distributions; linked through OpenSSH and other projects.
More from Veritasium
View all 96 summaries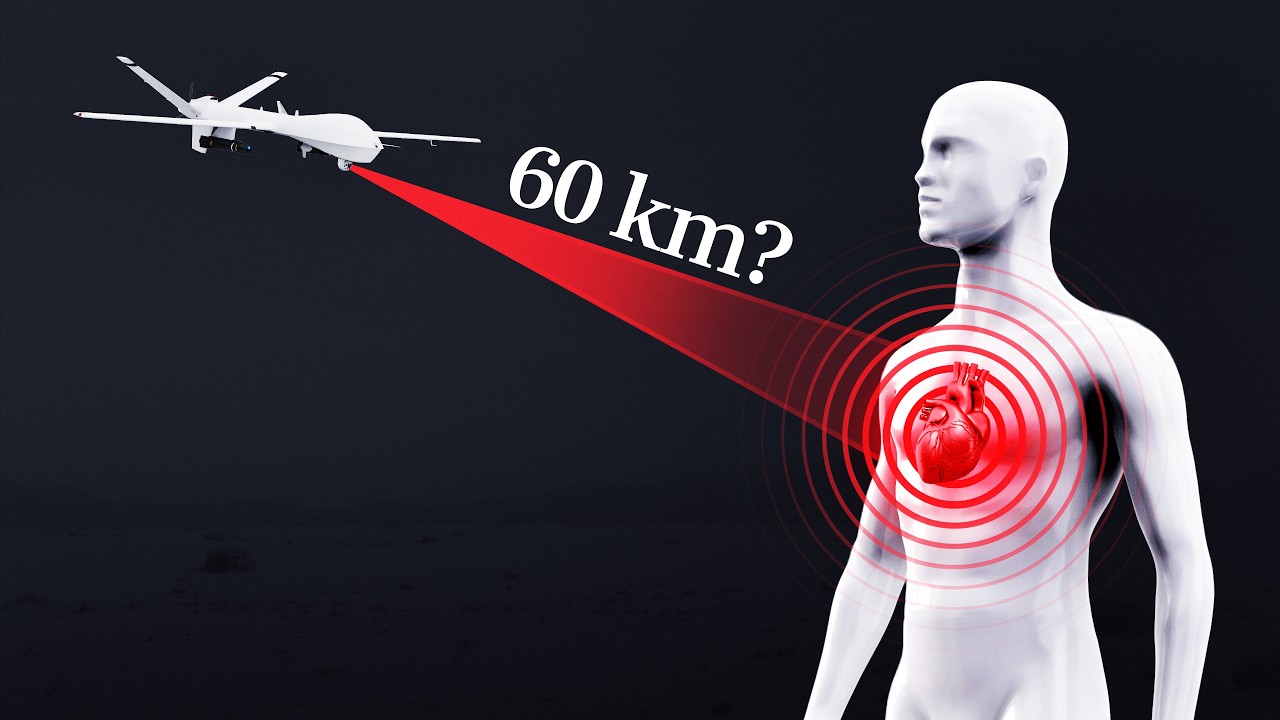 22 min
22 minCan a quantum sensor detect your heartbeat from 60 km away?
 34 min
34 minThe disaster I never imagined having to worry about
 27 min
27 minCan you steal $10,000 from a locked iPhone?
 59 min
59 minWhy Is CERN Making Antimatter?
Ask anything from this episode.
Save it, chat with it, and connect it to Claude or ChatGPT. Get cited answers from the actual content — and build your own knowledge base of every podcast and video you care about.
Get Started Free