Key Moments
Exposing The Flaw In Our Phone System
Want to know something specific about what's covered?
We've already dissected every moment. Ask and we will deliver (with timestamps).
Key Moments
The SS7 phone network has critical flaws, allowing remote interception of calls and texts.
Key Insights
The SS7 protocol, designed in the 1980s, has fundamental security vulnerabilities that allow widespread spying.
Attackers can intercept phone calls and text messages by exploiting SS7, enabling theft of two-factor authentication codes.
Location tracking is also possible via SS7, pinpointing users with surprising accuracy without GPS.
While newer protocols exist, SS7's widespread use in legacy systems (2G/3G) and its network effects prevent rapid replacement.
Personal protection includes using authenticator apps over SMS for 2FA and opting for encrypted calling services.
THE RISE OF BLUE BOXING AND EARLY EXPLOITS
The history of phone system exploitation began with 'blue boxes' in the 1970s. These devices hacked the telephone network to make long-distance calls for free, demonstrating early vulnerabilities. This era highlighted how a small group could manipulate vast infrastructure. The innovation stemmed from the need to automate manual call connections, leading to rotary dials and later, Touch-Tone phones. Each technological leap, while improving efficiency, also introduced new potential exploit vectors.
THE LIMITATIONS OF ANALOG AND THE BIRTH OF SS7
Early phone systems relied on analog signals. Clear control signals became distorted over longer distances, hindering long-distance automation. The introduction of Touch-Tone phones used tones within the voice band, solving the distance issue but creating new vulnerabilities. Notably, a 2600Hz tone could trick the network into thinking a call was disconnected, allowing free long-distance calls. This led to the development of Signaling System No. 7 (SS7), a separate digital line for control signals to enhance security and reliability.
SS7'S ARCHITECTURE AND GROWING VULNERABILITIES
SS7 was designed in an era dominated by a few trusted telecom operators. It uses Global Titles (GTs) for addressing, and networks generally trust messages from known GTs. This 'walled garden' approach assumed a closed, secure network. However, the landscape has dramatically shifted with over 4,500 networks globally, many of which are less trustworthy. Entities can now lease SS7 access for a few thousand dollars per month, creating numerous entry points for malicious actors.
THE THREE STEPS TO EXPLOITING SS7
Exploiting SS7 typically involves three key steps. First, infiltration, which is gaining access to the SS7 network, often through leased Global Titles. Second, gaining trust, which involves obtaining the target's phone number and uniquely identifying SIM card information like the International Mobile Subscriber Identity (IMSI). Third, the attack phase, where modified SS7 messages are sent to intercept calls, reroute text messages, or track location.
INTERCEPTING CALLS AND TEXT MESSAGES
Once SS7 access is secured and the target's IMSI is known, attackers can intercept calls and text messages. By tricking the network into thinking the target phone is roaming, calls can be rerouted to a number controlled by the attacker. This same technique allows for the interception of SMS messages, including crucial one-time passwords used for two-factor authentication (2FA). This capability poses a significant risk to online accounts, including financial services, as demonstrated by hacking a YouTube account.
LOCATION TRACKING AND REAL-WORLD CONSEQUENCES
Beyond communication interception, SS7 enables sophisticated location tracking. By sending specific commands to the switching center connected to a user's device, attackers can determine the cell tower a phone is connected to, providing location accuracy down to a city block. This has been used to track individuals, including public figures. The Princess Latifa case highlighted how SS7 attacks, combined with other surveillance tools, could be used to locate and abduct individuals, demonstrating the severe real-world consequences of these vulnerabilities.
THE ENDURING CHALLENGE OF SS7 REPLACEMENT
Despite its known flaws, SS7 remains the backbone for 2G and 3G communications. Newer, more secure protocols exist for 4G and 5G networks, but widespread adoption is hindered by network effects and the need for legacy support. Many critical systems, like mandatory emergency call buttons in cars, still rely on older technologies. Consequently, SS7 is likely to persist for many years, estimated to be another 10-20 years, despite ongoing exploits and the availability of more secure alternatives.
PERSONAL PROTECTIONS AND THE IMPORTANCE OF KNOWLEDGE
While individual protection against SS7 exploitation is limited, users can take steps to mitigate risks. It's advised to avoid SMS-based two-factor authentication whenever possible, opting instead for authenticator apps or hardware tokens. For calls, encrypted internet-based services like Signal or WhatsApp offer greater privacy. Ultimately, the video emphasizes that building knowledge and problem-solving skills is the best defense in an ever-evolving technological landscape, empowering individuals to understand and navigate complex issues like SS7 vulnerabilities.
Mentioned in This Episode
●Products
●Software & Apps
●Companies
●Organizations
●Concepts
●People Referenced
Protecting Yourself from SS7 Vulnerabilities
Practical takeaways from this episode
Do This
Avoid This
SS7 Attack Costs and Vulnerabilities
Data extracted from this episode
| Item | Cost/Description | Vulnerability/Impact |
|---|---|---|
| SS7 Connection | Few thousand per month | Allows access to the global SS7 network. |
| Leased US-based GT | $113,000 per month | Illegal leasing demonstrates risk of trusted access. |
| Zero-click hacks (Pegasus) | Over $4 million per exploit | Advanced surveillance, gains complete phone access. |
| Malicious SS7 Requests | Millions per year | Tracking and potential interception attempts. |
| SS7 Location Tracking | Identifies cell tower connection | Places target within ~100m in urban areas. |
| Spyware (Pegasus) Purchase | Costly, requires specific data | Targets specific software/vulnerabilities after gathering device info. |
| Pre-2014 SS7 Location | Anytime Interrogation Request | Provided location without knowing IMSI; largely deprecated but indicative of past risks. |
Common Questions
Attackers exploit SS7 vulnerabilities to trick the network into thinking a phone is roaming, rerouting calls and messages to their control. This allows them to intercept communications and steal sensitive information like two-factor authentication codes.
Topics
Mentioned in this video
A YouTube channel or entity that calls Lonus as part of the demonstration, unknowingly connecting to Derek.
The YouTube channel producing this video, with Derek as a host or representative.
Mentioned as the source of parts used to build early phone hacking devices like the blue box.
An Israeli cyber surveillance firm known for developing spyware like Pegasus and acquiring SS7 tracking companies.
Cybersecurity specialist who assists in demonstrating SS7 attack methods.
Princess Latifa's Finnish martial arts instructor, who helped her attempt to escape.
Former French intelligence officer and captain of the yacht Princess Latifa used to escape.
Member of the Dubai royal family whose escape and subsequent abduction highlight the dangers of SS7 exploits.
US Congressman who was tracked using SS7 location methods by researchers.
Cybersecurity specialist who assists in demonstrating SS7 attack methods.
Ruler of Dubai and father of Princess Latifa, implicated in her detention and the use of surveillance technology.
Unique addresses used in SS7 to identify where network requests are coming from, analogous to IP addresses on the internet.
A protocol used for call setup, control, and other services in telecommunication networks, which is known to have significant security vulnerabilities.
A unique 15-digit identifier belonging exclusively to a SIM card, crucial for identifying and targeting mobile subscribers in SS7 attacks.
More from Veritasium
View all 97 summaries 30 min
30 minHow Does Google Maps Actually Work?
 22 min
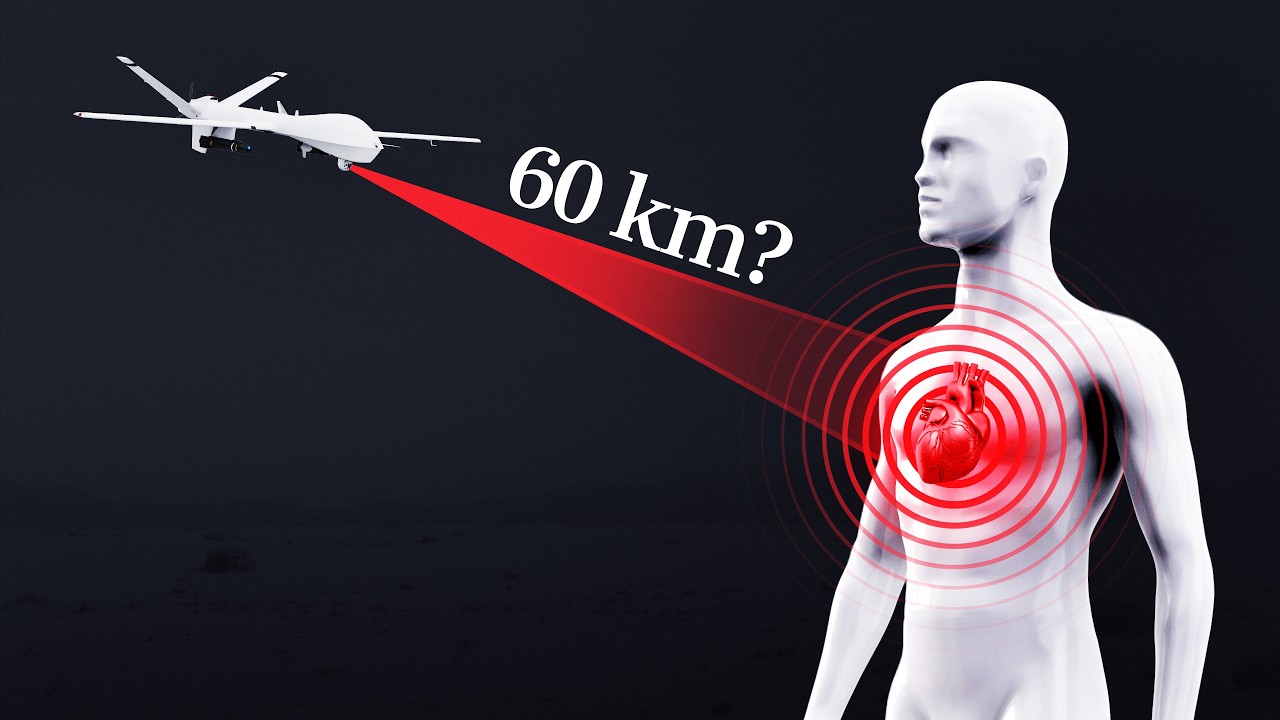
22 minCan a quantum sensor detect your heartbeat from 60 km away?
 34 min
34 minThe disaster I never imagined having to worry about
 27 min
27 minCan you steal $10,000 from a locked iPhone?
Ask anything from this episode.
Save it, chat with it, and connect it to Claude or ChatGPT. Get cited answers from the actual content — and build your own knowledge base of every podcast and video you care about.
Get Started Free